An NPI mismatch is a leading trigger associated with payer enrollment audits in 2026. As the healthcare landscape becomes increasingly digitized, the margin for administrative error has narrowed. Federal agencies and private payers use increasingly sophisticated data-validation tools to identify discrepancies across enrollment records and claims activity. If your practice is operating on "stale" data, you are not just at risk for a claim denial: you are increasing the likelihood of a comprehensive payer enrollment review that can disrupt your revenue cycle.
Looking for professional provider credentialing services in the USA?
👉 Check our main service page here: veracityeg.com
At The Veracity Group, we have observed heightened audit and review activity throughout the first half of 2026. The shift is clear: according to observed industry trends and payer reporting patterns, payers such as UnitedHealthcare, Aetna, and Cigna are relying more heavily on data comparison and exception-based review workflows. They are cross-referencing internal claims data against enrollment and identity records with increasing precision. If your provider enrollment records do not align across every platform, the file can be flagged for an "integrity review" or manual follow-up.
The 58% Inaccuracy Trap: Why the OIG is Watching
The Office of Inspector General (OIG) previously noted a staggering 58% inaccuracy rate in federal provider identity databases. In response, CMS has tightened the screws on data synchronization. In 2026, the discrepancy between your NPPES (National Plan and Provider Enumeration System) profile and your PECOS (Provider Enrollment, Chain, and Ownership System) record is the leading "silent trigger" for audits.
When these two systems are out of sync, they can signal weak internal controls and elevate scrutiny during enrollment review. This is more than a clerical error; it is often treated as a compliance concern. Payers and regulators use basic identity-data consistency as a baseline indicator of whether your organization is maintaining reliable administrative documentation.
The NPI Mismatch: Type 1 vs. Type 2 Red Flags
The most common technical trigger involves the misuse of NPI Type 1 (Individual) and NPI Type 2 (Organizational) identifiers. We frequently see practices submit claims using a provider's individual NPI where the group's organizational NPI is required: or vice versa.
In the 2026 audit environment, payers use automated rules to identify these mismatches quickly. If your payer enrollment file lists a provider at Location A under a specific Tax ID, but the claim comes in with an NPI associated with Location B, the discrepancy can do more than deny the claim; it can trigger broader review of your enrollment history. This is why demographic updates are no longer a "when we get to it" task: they are a weekly necessity.

Visual Description: A forensic, high-contrast image in cinematic navy and amber tones showing a digital magnifying glass hovering over a complex grid of NPI numbers and provider data points.
The Standard 30-Day Reporting Window: A Major Compliance Risk
Failure to report location changes within a standard 30-day reporting window is a major audit risk factor in 2026. CMS and major private payers closely monitor for "ghost locations": addresses listed in directories where the provider no longer practices.
If a patient attempts to schedule an appointment at a location listed in the directory and finds the provider has moved, and that patient files a complaint, an audit risk escalates sharply. Based on observed industry reports and directory-accuracy enforcement trends, UnitedHealthcare and Aetna have applied increased scrutiny to provider directory verification. If your practice has added a new suite, closed a satellite office, or moved across the street, and that change was not reflected in your provider enrollment files within the payer's required timeframe, you are increasing your exposure under payer contract terms.
Stale CAQH Profiles: The Gateway to Revenue Disruption
Your CAQH profile is the backbone of your professional credibility with private payers. However, many practices treat CAQH as a "set it and forget it" platform. In 2026, a stale CAQH profile: one that has not been re-attested or updated with current malpractice insurance, DEA certifications, or state licenses: is a serious risk factor for payment disruption, manual review, or audit escalation.
Payers are now performing "cross-system data scrubs." They compare your CAQH data to state licensing boards and other available verification sources. If a mismatch occurs, the payer will often initiate an audit or manual review to determine whether claims were paid based on inconsistent provider data. To avoid this, you must understand what every practice manager needs to know about CAQH updates.
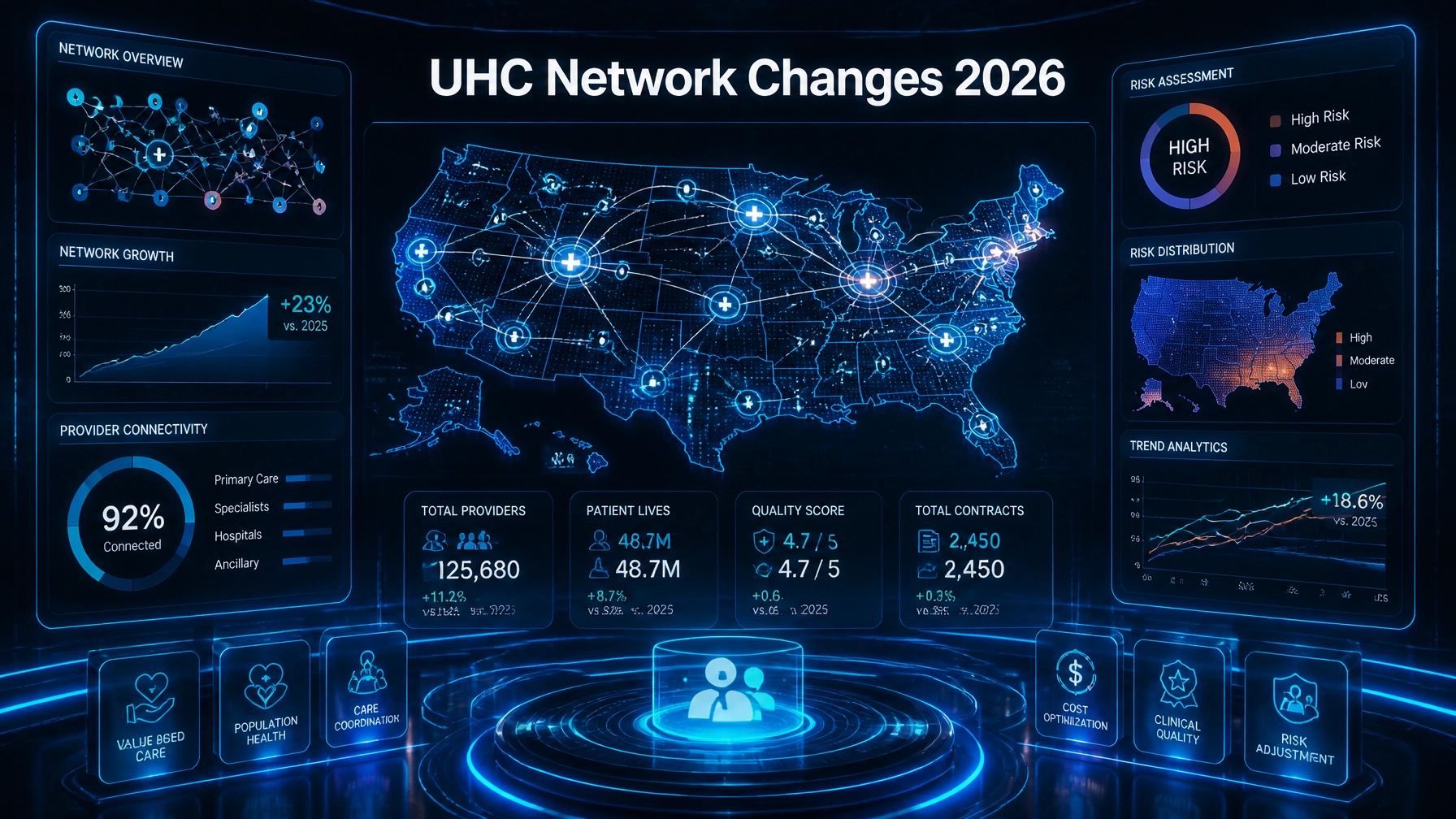
Forensic Scrutiny from the "Big Three": UHC, Aetna, and Cigna
In 2026, observed industry trends indicate that the "Big Three" private payers are placing greater attention on administrative outliers during audit and enrollment review activity. They are not just looking for fraud; they are also looking for data inconsistencies that create network and payment risk.
- UnitedHealthcare: Industry reports suggest increased scrutiny when billing patterns do not align with an enrolled specialty or expected scope of practice.
- Aetna: Observed payer behavior indicates a strong focus on "network integrity," including address-standardization and directory-accuracy issues.
- Cigna: Industry reports indicate heightened attention to provider directory fields such as practice status and panel availability when those fields affect member access data.
This level of scrutiny makes it imperative to stay informed on Medicare and Medicaid enrollment trends for 2026, as private payers often mirror broader federal data-integrity priorities.

Visual Description: A tech-forward, cinematic image in amber and deep navy showing a stylized dashboard of healthcare audit "red flags" and flashing warning symbols over a map of provider networks.
How to Build an "Audit-Proof" Enrollment Strategy
Survival in the 2026 healthcare market requires a proactive, defensive stance. You cannot afford to wait for a letter from a payer to realize your data is compromised.
- Synchronize NPPES and PECOS: Ensure your legal name, Tax ID, and primary practice location match exactly across both federal databases. Even a missing "Suite" number or a hyphen in a name can trigger a manual review flag.
- Conduct a 90-Day Data Scrub: Every quarter, perform a comprehensive review of all provider data. This includes verifying that every provider’s medical licensing, CSR, and DEA information is current and matches their CAQH profile.
- Validate NPI Types: Double-check that your billing software is correctly utilizing Type 1 and Type 2 NPIs according to each specific payer’s requirements.
- Monitor the 30-Day Clock: Implement a strict internal policy where any change in practice location, phone number, or tax identity is reported to all payers within 15 days, providing a 15-day buffer before common payer reporting deadlines.
The Cost of Inaction: More Than Just a Fine
A payer enrollment audit is a resource drain. It pulls your administrative staff away from revenue-generating tasks and places your practice under a microscope for months. The ultimate consequence is not just a fine; it can include payment delays, corrective action demands, or even termination of your payer contract, depending on the severity of the issue and the payer's contract terms. Once you are removed from a network due to compliance failures, getting back in is an uphill battle that many practices do not survive.
If you are already seeing credentialing delays, take it as a warning sign. Delays are often the precursor to a deeper inquiry into your data's validity.
Conclusion: Your 2026 Enrollment Standard
The era of "close enough" in provider data is over. In 2026, precision is the strongest protection against payer audits and enrollment disruption. By maintaining a forensic level of detail in your NPPES, PECOS, and CAQH profiles, you help ensure that your practice remains a "green flag" in a sea of administrative errors.
CTA: If you have not performed a cross-system data scrub in the last 90 days, perform a 10-provider audit this week. Identify one NPI mismatch or one stale address, and you will have addressed a major audit risk before it grows into a larger problem.
Looking for professional provider credentialing services in the USA?
👉 Check our main service page here: veracityeg.com
#HealthcareCompliance #ProviderEnrollment #MedicalBilling #NPI #PayerAudit #CMS #CAQH #HealthcareAdmin #RevenueCycleManagement #MedicalPracticeManagement #Credentialing #PECOS #NPPES #HealthcareData #Aetna #Cigna #UHC #AuditDefense #MedicalCompliance #PracticeSuccess #HealthTech2026 #DataIntegrity #HealthcareConsulting #EnrollmentAudit #TheVeracityGroup